W32.AIDetectVM.malware — что это за вирус?

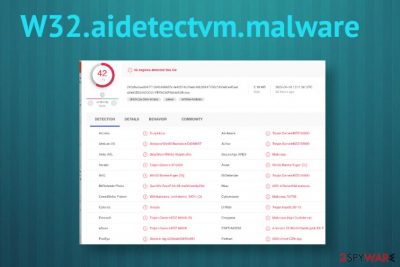
PS: VirusTotal — известный популярный сервис, где можно проверить любой файл на наличие вирусов. Для проверки будут использованы десятки антивирусных движков (в том числе малоизвестных).
W32.AIDetectVM.malware — что это такое?
Угроза, которая может быть найдена антивирусом Bkav в проверяемом файле на VirusTotal.
W32 скорее всего означает что приложение 32-битное, а malware означает просто вредоносная программа. AIDetectVM — непонятно.
W32.AIDetectVM.malware может обнаруживаться в любом софте/файле. Читал сообщения, что находили в установщиках игр и даже в ПО Java, скачанном с офф сайта.
Пишут что антивирусный движок Bkav во многих нормальных программах находит угрозу W32.AIDetectVM.malware. Другими словами — ложная тревога.
Bkav возможно и неплохой. Однако о нем мало слышно на рынке СНГ в отличии от Avast, Kaspersky, NOD32.
W32.aidetectvm.malware
W32.aidetectvm.malware
W32.aidetectvm.malware is a Trojan Horse infection that can take advantage of system security flaws. Once inside the computer, W32.aidetectvm.malware can spy on its victims and execute different malicious activities without being detected.
W32.aidetectvm.malware Trojan Horse
The Trojans are terrible threats and there hardly is a form of malware more versatile than them. But what to do if you are faced with an infection from a Trojan Horse type? Many web users tend to get panicked and have no idea how to deal with such malware. That’s why we’ve decided to provide some useful information about the Trojans here and more specifically about W32.aidetectvm.malware, as one of their latest representatives. Some of our readers have had the misfortune of landing this virus and have contacted our “How to remove” team to ask for a solution. That’s why you will find a detailed removal guide just below this article with instructions on how to manually remove W32.aidetectvm.malware from your system. Of course, you can also use the professional anti-malware software attached to the guide to quickly scan your device and get rid of the Trojan in a matter of minutes. But before you move to it, here’s some more information about what to expect from such infections and how to protect your system in the future.
Trojan Horses’ destructive abilities.
The first thing people want to know once they’ve discovered a Trojan Horse on their machine is what kind of damage this malware can do. And there couldn’t be a more varied list of malicious actions when it comes to the abilities of this particular category of malware. First of all, the reason such programs are called Trojans is because they invade your machine through stealth. They typically act as a harmless file or a useful program that tricks you into downloading and installing it. Once inside the system, the Trojans can be set by the hackers behind them to accomplish a certain criminal task. What this task is depends on what the cyber criminals seek to accomplish with this particular virus.
For example, they can set an infection like W32.aidetectvm.malware to steal data from you. This is perhaps one of the most common uses and can be accomplished using a variety of techniques. The Trojan can record your keystrokes, monitor the activity on your screen, or maybe transfer files from your system to the hackers’ servers. The crooks can, thereby, gain access to sensitive information like passwords, login details, banking details, etc.
Another common way cybercriminals employ Trojans is for the distribution and insertion of other malware inside the attacked computer. A threat like W32.aidetectvm.malware can exploit vulnerabilities of the system, such as outdated software, the absence of a security program, or some badly written code to secretly insert a Ransomware, a Spyware, or another virus without the victim’s knowledge. It can also manipulate the resources of your machine for a number of purposes, including sending out spam within your network. This all comes to show that the Trojans really are among the most dangerous pieces of malicious code out there. And that’s why it’s important that you remove W32.aidetectvm.malware from your computer as quickly as possible. It is no less important that you protect your system from such threats with reliable security software. For that, you must update your system and all the programs on it that need to be updated to make sure there are no system vulnerabilities that can be exploited.
SUMMARY:
| Name | W32.aidetectvm.malware | |||||||||||||
| Type | Trojan | |||||||||||||
| Detection Tool |
| Name | W32.aidetectvm.malware |
|---|---|
| Type | Malware/ AV detection result |
| Possible outcome | This detection can be falsely positive and lead to anything besides compromised files or programs. However, the detection indicates trojans or different type of computer virus that may modify system files or open backdoors for remote attackers, install additional threats like ransomware and so on |
| Distribution | Many malicious websites can trigger downloads of these intruders and files attached to spam emails can drop the code of the malware. There are many ways to deliver these kinds of files because malware can run in the background without causing any symptoms after a visit on the shady domain or insecure freeware download |
| Danger | This program can be designed to drop additional script or malware directly on the machine and furthermore infect the system. malware can open backdoors to remote attackers that directly control your machine and uses the device as a tool for different campaigns |
| Elimination | W32.aidetectvm.malware removal should be the best when you delete the intruder using a particular AV tool that detected this malware in the first place |
| Repair | For the proper system cleaning, you should repair corrupted files and get rid of the virus damage or any associated files and programs, so run the Reimage Intego or a similar PC utility that can indicate files in need for fixing |
W32.aidetectvm.malware is possibly a false positive result that is not related to any intruder or issues on your device, but AV tools are designed to detect and indicate possibly dangerous or even malicious programs, files, and even sites where user can get exposed to malware-laced material.
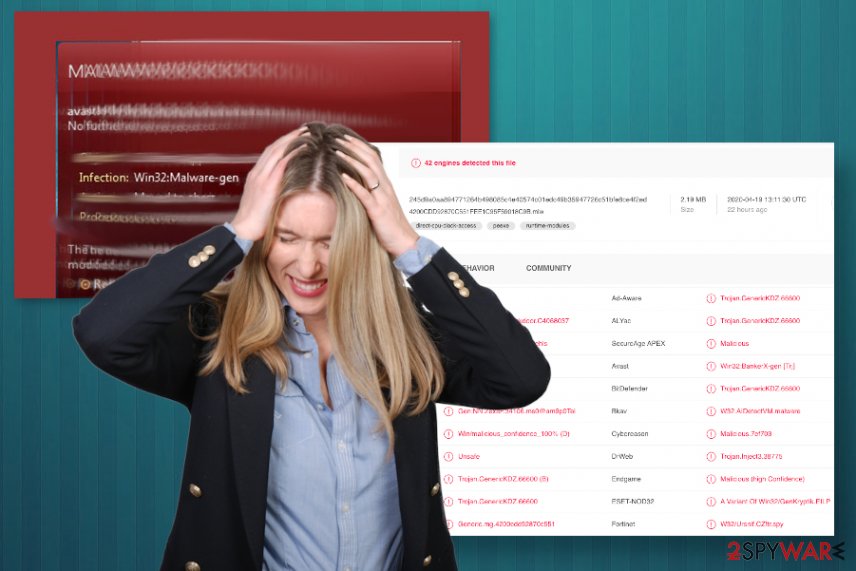
However, detection results and pop-up alerts with results like this can appear all the time, if that is the case, you should react and try to remove W32.aidetectvm.malware as soon as possible. The best results can be achieved with a tool that warned you about the danger, in the first place. Your machine may perform poorly due to occurring pop-up alerts alone, so the sooner you find a solution, the better.
If W32.aidetectvm.malware virus appears to be a trojan or a different type of dangerous computer virus, it can:
W32.aidetectvm.malware may run in the background and reinstall itself to keep the persistence up. Such stealthy threats aim to take advantage of the system, exploiting various flaws, and once important parts get affected, the virus can spy on victims directly or execute any codes without the indication that there is an intruder. This fact that trojan can run undetected for a while makes it more dangerous and damaging.
You should consider that when you focus on W32.aidetectvm.malware removal because when the threat has its roots deep in the system, all associated applications and files need to be deleted to remove the infection fully. For this purpose. experts [3] always recommend going for proper system tools like Reimage Intego that can also repair damaged files, affected or corrupted programs for you when the detection is falsely positive due to incompatibility issues, for example.
W32.aidetectvm.malware is the generic detection name that appears on warnings and alerts from the anti-malware tools. W32.aidetectvm.malware can be set to do a handful of processes and have many features that usually are affecting the system significantly, but cannot be noticed in time. Malware like trojans or worms can execute commands that expose the machine to a malicious actor or run the additional script of threats like ransomware and cryptomining viruses.
The name of the trojan virus comes from the ability to invade the system silently, so the infection can run for a long time until you notice anything disturbing or the AV tool that you use indicates W32.aidetectvm.malware as a possible issue. Malicious actors behind the threat can aim yo gain access to sensitive information stored on your device or even target passwords, credentials, other login details. banking account data.
Personal information is one of the more valuable things that malware creators may design their products to gather. W32.aidetectvm.malware can be a tool used to achieve particular tasks of cybercriminals. Since cryptocurrency is the second thing that malicious actors may focus on, you may receive a virus that runs on the resources of the machine and generates Bitcoins for the creator.
Once trojans end up on the computer, it is possible to get a ransom-demanding malware that directly blackmails money from you. The most important thing is to react as soon as possible and clean the machine fully from all the threats, so there is no opportunity for W32.aidetectvm.malware or any other virus to repeat the infection in the future.
Stay away from suspicious materials to avoid malware infections
Most of the threats that are based on stealthy infiltration and silent background processes get distributed with the help of malicious files. However, malware-laced file distribution techniques also can differ. Various web pages and sites that are harmful replicas of legitimate pages and sites designed exceptionally for malware distribution can drop files with malicious scripts on your device and lead to serious issues immediately after that.
Also, stay away from spam emails and notifications received from unknown sources, senders that resemble companies or services that you don’t use or rely on. Such emails include links to those malicious pages or direct files like documents or executables that rigger the launch of a virus script. Always scan the attachment with the malware protection tool before loading it on the machine.
You should also pay attention to the content you visit willingly, sites that you rely on for software downloads, and other purposes. Read the license agreements and privacy statements of sites that become the source of your applications. downloading anything from operating services and untrustworthy sites can lead to serious problems with the machine and even result in identity theft or money loss.
W32.aidetectvm.malware infection need to get terminated using proper AV tools
You may think that the W32.aidetectvm.malware virus is damaging your machine the minute you receive an alert with the name of this intruder, but the infection might not even happen when the detection is falsely showing up on the computer screen. This is the threat that can possibly infect Windows devices, but there are not many symptoms that users can notice.
The first reason that should be a red flag and make you want to remove W32.aidetectvm.malware is the general performance of the machine that gets affected by the trojan because the computer starts running slow and crash from time to time. You need to be cautious and pay attention to any system performance changes, so run the AV tool to found out what is wrong.
If you use professional anti-malware tools already, W32.aidetectvm.malware removal shouldn’t be difficult or cause any issues for you. The detection with this particular name can indicate various threats, so when you run SpyHunter 5 Combo Cleaner or Malwarebytes, and the result shows up, you need to follow the steps and clean the machine from the malware yourself.
After all these processes, you should also use Reimage Intego for the help with possible damage or corrupted files that may be the initial reason why you see the alert about a possible security issue that may not even exist.